On August 24, 2024 a Hacker dumped 2.7 Billion data records, including Social Security Numbers
The data is alleged to be taken from the background-checking service National Public Data in April, 2024. Each one of the records has a person’s name, physical address, mailing address, and SSN, but many (approximately 1/2) also contain other sensitive information, such as names of relatives as well as their personal identifying information; including SSN’s according to many sources.
A new lawsuit is claiming hackers have gained access to the personal information of “billions of individuals,” including their Social Security numbers, current and past addresses and the names and even social security numbers of siblings and parents — personal data that could allow fraudsters to infiltrate financial accounts or take out loans in their names.
The allegation arose in a lawsuit filed earlier this month by Christopher Hofmann, a California resident who claims his identity theft protection service alerted him that his personal information had been leaked to the dark web by the “nationalpublicdata.com” breach. The lawsuit was first reported by Bloomberg Law.
The breach allegedly occurred around April 2024, with a hacker group called USDoD exfiltrating the unencrypted personal information of billions of individuals from a company called National Public Data (NPD), a background check company based in Florida, according to the lawsuit. Earlier this month, a hacker leaked a version of the stolen NPD data for free on a few hacking forums as well as other sites.
Background & Context:
This breach is related to an incident from April 8, 2024, when a known cyber-criminal group named USDoD claimed to have access to the personal data of 2.9 billion people from the U.S., U.K., and Canada and was selling the information for $3.5 million, according to a class action complaint. USDoD is thought to have obtained the database from another threat actor using the alias “SXUL.”
This data was supposedly stolen from National Public Data, also known as Jerico Pictures, and the criminal claimed it contained records for every person in the three countries. At the time, the malware website VX-Underground said this data dump does not contain information on people who use manual data opt-out services. “Every person who used some sort of data opt-out service was not present,” it posted on X.
A number of cyber criminals then posted different samples of this data, often with different entries and containing phone numbers and email addresses. But it wasn’t until earlier this month that a user named “Fenice” leaked 2.7 billion unencrypted records on the dark web site known as “Breached,” in the form of two .CSV files totaling 277GB. These did not contain phone numbers and email addresses, and Fenice said that the data originated from SXUL.
Furthermore, according to GeeksByTheHour, approximately 1/4 of the impacted individuals we have spoken to have confirmed that the SSN associated with their info in the data dump is actually ONE OF THEIR CLOSE RELATIVES, probably because of the way background check data providers such as this one gather any and all data not just from the person being investigated, but also close relatives.
GeeksByTheHour also found that some of the records do not contain the associated individual’s current address, suggesting that at least a portion of the information is out of date. But it is important to note that documentation has been found that these records include THIRTY (30) YEARS of data (January, 1994 – April, 2024). However, others that GeeksByTheHour have reached out to have confirmed that the data contained their and family members’ legitimate information, including those who are deceased.
The class action complaint added that National Public Data scrapes the personally identifying information of billions of individuals from non-public sources to create their profiles. This means that those impacted may not have knowingly provided their data. Those living in the U.S. are particularly likely to be impacted by this breach in some way. Why? Because of the culture of huge data revealing practices that the U.S. takes for granted. One of these is one’s sharing their SSN to any and all “merchants” and hospitals and companies for, as an example, a Credit Check.
AT & T (most recently in 2024) is far from being the only company that have had significant breaches of personal identifying information.But we can start with that one due to it being the most recent: AT & T determined the data was from 2019 or earlier and impacted 7.6 million current account holders and 65.4 million former account holders. In that case, personal information of users, such as Social Security numbers, email addresses, mailing addresses, AT&T account numbers, phone numbers and more were obtained in the beach, AT&T said.
T-Mobile was a victim: T-Mobile has disclosed eight hacks since 2018, with previous breaches exposing customer call records in January 2021, credit application data in August 2021, and an “unknown actor” accessing customer info and executing SIM-swapping attacks in December 2021. In April, 2023, the hacking group Lapsus$ stole T-Mobile’s source code after purchasing employees’ credentials online.
Equifax, one of the big 4 credit bureaus and several other companies that have your most identifying information have all publicly come forward revealing they, along with one’s most personal and private data; have been significantly compromised.
2017 Equifax data breach:
Experts who GeeksByTheHour spoke to suggest that individuals impacted by the breach should consider monitoring or freezing their credit reports and remain on high alert for phishing campaigns targeting their email or phone number.
Businesses should ensure any personal data they hold is encrypted and safely stored. They should also implement other security measures such as multi-factor authentication, password managers, security audits, employee training, and threat-detection tools.
GeeksByTheHour has reached out to Florida-based National Public Data for a response five separate times since the rumors began on the internet (July, 2024). This includes physically visiting their publicly listed office building, where no one answered the buzzer at the front door after several attempts at different times this week. However, it has yet to acknowledge the breach or inform impacted individuals. The existing details about the incident have been extracted from the lawsuit materials, and the company is currently under investigation by Schubert Jonckheer & Kolbe LLP.
GeeksByTheHour Analysis:
So how does a firm like National Public Data obtain the personal data of almost 3 billion people? The answer is through scraping – which is a technique used by companies to collect data from government sources (such as DMV leaked records), web sites and other sources online.
What makes the way National Public Data did this more concerning is that the firm scraped personally identifiable information (PII) of billions of people from non-public sources. As a result, many of the people who are now involved in the class action lawsuit did not provide their data to the company willingly.
Why are the National Public Data records so valuable to cyber criminals? The true core value of the National Public Data records from a criminal’s perspective comes from the fact that they have been vetted, verified to be accurate, collected and organized along with “legitimate” data and PII (Personal Identifying Information).
“While the information is largely already available to attackers, they would have had to go to great lengths at great expense to put together a similar collection of data, so essentially NPD just did them a favor by making it easier.”
“With this ‘starting point,’ an individual can try to create birth certificates, voting certificates, driver licenses, ID cards, etc., that will be valid due to the fact they have some of the info they need, with the most important one being the social security number.”
How can data aggregator breaches be stopped?
Paul Bischoff, consumer privacy advocate at tech research firm Comparitech, told Dr. Sky in an email, “Background check companies like National Public Data are essentially data brokers who collect as much identifiable information as possible about everyone they can, then sell it to whomever will pay for it. It collects much of the data without the knowledge or consent of data subjects, most of whom have no idea what National Public Data is or does”.
“We need stronger regulations and more transparency for data brokers that require them to inform data subjects when their info is added to a database, limit web scraping, and allow data subjects to see, modify, and delete data. National Public Data and other data brokers should be required to show data subjects where their info originally came from so that people can take proactive steps to secure their privacy at the source. Furthermore, there is no reason the compromised data should not have been encrypted.”
“The monetization of our personal information — including the information we choose to expose about ourselves publicly — is far ahead of legal protections that govern who can collect what, how it can be used, and most importantly, what their responsibility is in protecting it.”
Can businesses and individuals prevent themselves from becoming victims of a data breach?
Many of the cyber security principles that are available for businesses and individuals would not have helped much in this instance. As of 2024, data brokers such as this one are pretty much immune unfortunately.
“We are reaching the limits of what individuals can reasonably do to protect themselves in this environment, and the real solutions need to come at the corporate and regulatory level, up through and including a normalization of data privacy regulation via international treaty. Right now, there are very little to no regulations or laws for these Data Brokers.” (August, 2024).










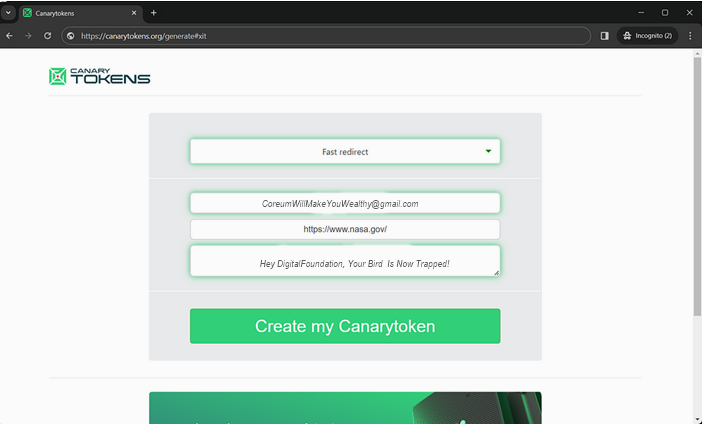
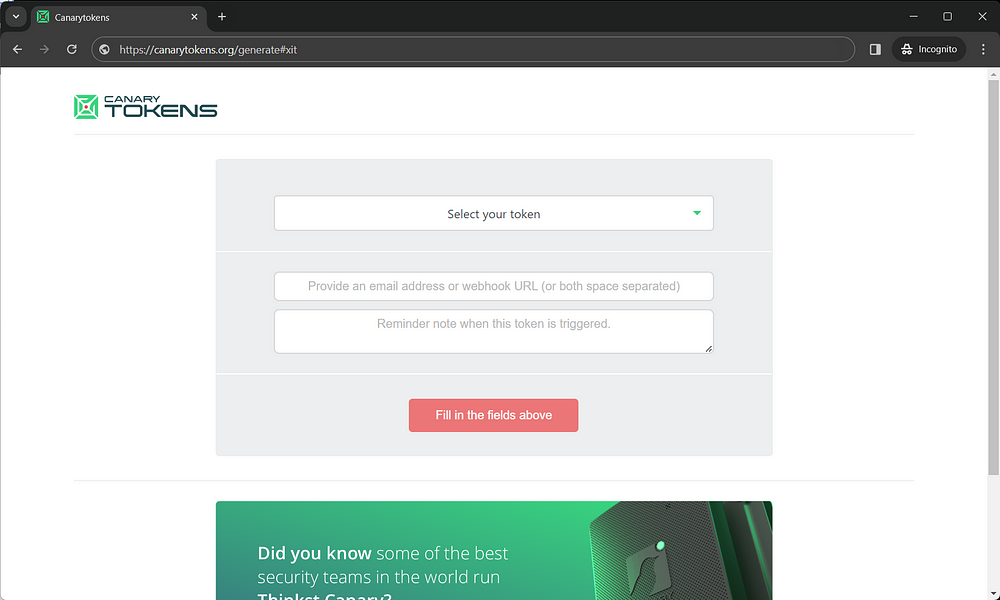
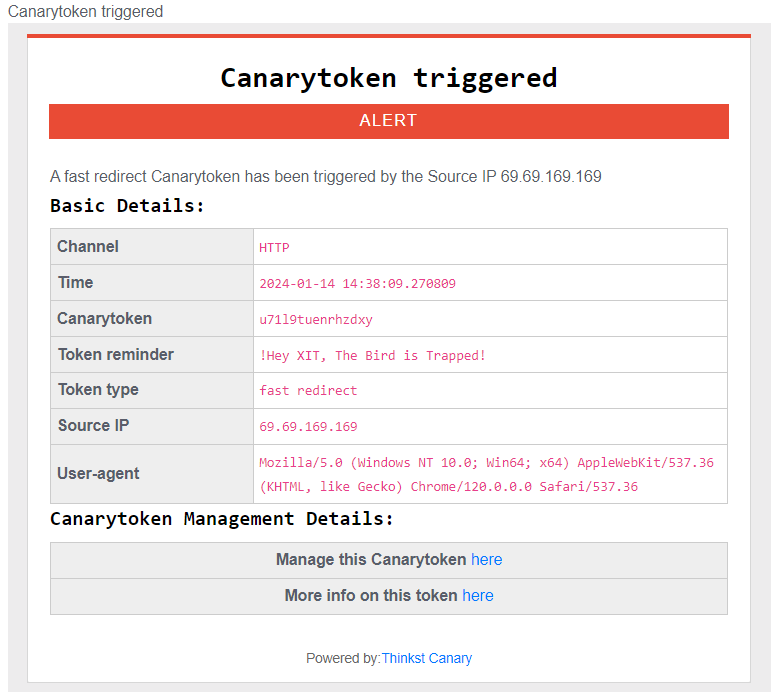
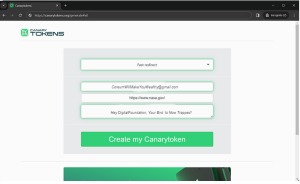 EXAMPLE
EXAMPLE