Why I ditched Gmail for Proton Mail
Chris Thomas
Google is the most popular email provider (Gmail) contributes about 70% of the email traffic on earth and being one of the oldest mass adopted email service (passing 20 years old is a worth achievement for any application, especially a “free” one.
As a cyber security digital expert, I have raved about the free service, its novel cloud-based structure, and how and why is
While I’m tickled to have been an early adopter of now-successful technology, though, it’s important to know when enough is enough. For me, that time has come, and I’m moving my primary digital correspondence to privacy-focused Swiss provider Proton Mail. It’s been a long time coming.
Should I, or should I not be popular?
Google is a Mega Monopoly Email Provider: Legal, but is it Ethical?
We’ve seen a lot go down in the privacy and security realms over the last two decades. Google’s been far from the only culprit, but as the default search engine for most browsers and the curator of Android, the Play Store, Google Analytics, reCaptchas, and more, the Big G has more data on the average North American user than any other corporation.
I’m as far from paranoid as any internet user, and even I use a VPN (primarily for spoofing IP geolocation); while I don’t do anything nefarious, and nobody’s tracking me for anything other than advertising, I prefer knowing I’m a little safer from bad actors that can hijack the content I’m viewing and thus possibly my hardware.
But Google creeps me out, and I’m no longer comfortable using Gmail. The successors to the FAANG stocks, the MAMAA companies (Meta, Apple, Microsoft, Amazon, and Alphabet) own a considerable amount of not just forward-facing web resources but also the underlying infrastructure most of the world’s internet relies on. I can’t avoid my data passing through the Google Cloud or Amazon Web Services, but I can limit what sites and apps I actively engage with.
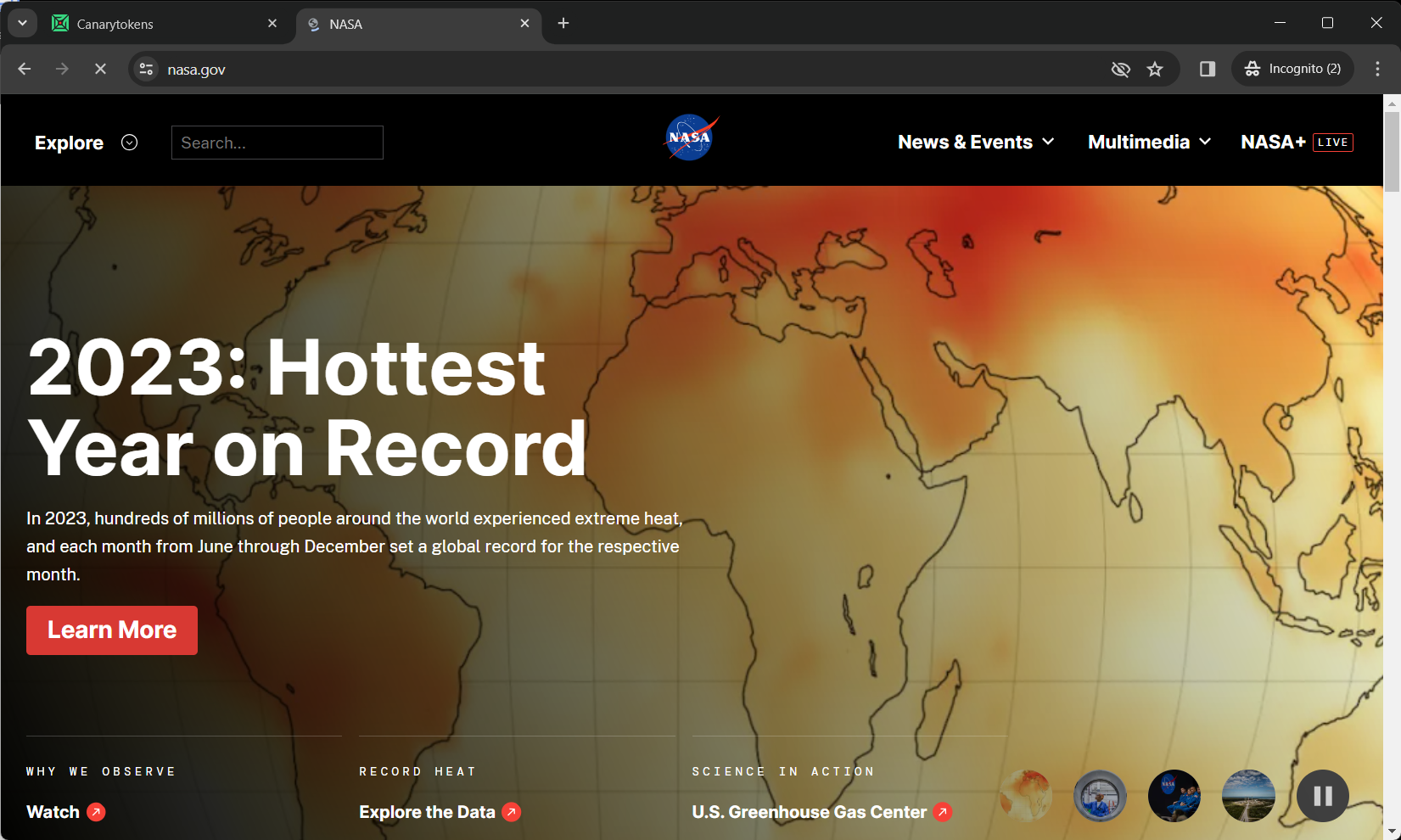
Gmail’s interface is fine, I guess, if somewhat cluttered and not very attractive
Google’s always innocent until it’s not
Until 2017, Google automatically scanned Gmail accounts for keywords that it then used to personalize ads within the platform and probably outside it, too. Here’s why that should terrify you:
- It had likely been happening since Gmail’s launch
- Scans included messages from non-Gmail accounts, presumably contributing to shadow accounts containing data on those users
- Widespread publicity via a 2013 Microsoft ad campaign and lawsuit the same year failed to stop it
- Google’s proposed settlement was rejected for being overly vague and failing to promise proper disclosure of data harvesting practices
- What else is Google doing that we haven’t learned about?
I’m under no misconception that I can extricate myself entirely from Google’s clutches; It’s too ubiquitous, and tons of common apps and services rely on its wide range of services. But I’ll do what I can, which includes moving to Proton Mail, a privacy-centric email provider with encrypted, underground servers, practically the polar opposite of Alphabet Inc.
Google paid over $26 billion in 2021 to remain the default search engine in various browsers
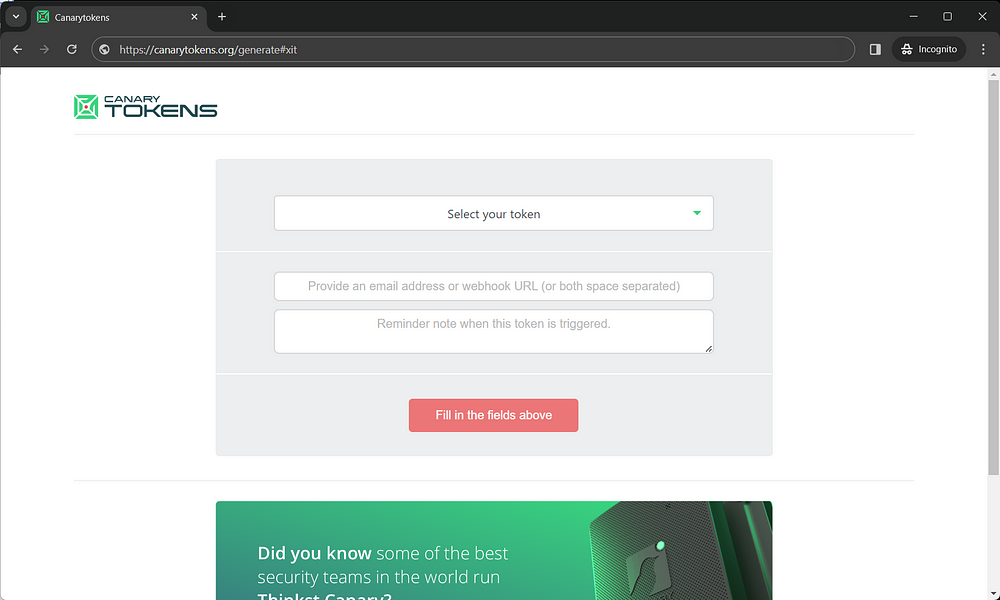
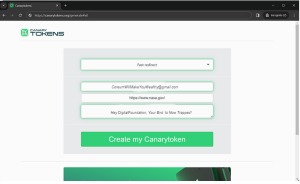
The surprisingly easy switch to Proton Mail
Why Proton Mail is my new favorite email provider
My own Proton account has been used as a backup since 2018. Moat recently though, it has now become my primary email for both personal and business.
I tested a trial of ProtonVPN a few years afo (ProtonVPN was a bit slow back then, but I and other cyber security expert highly recommend it as one of today’s top VPNs) due to its increased infrastructure and massive much faster speed. They have quadrupled the number of Servers globally since 2021).
I made the jump many years ago (2018) and highly recommend it to all of you going forward – primarily due to Proton’s comprehensive set of features, as well as the policies it enacts to keep your data private.
Among Proton’s consumer-friendly practices:
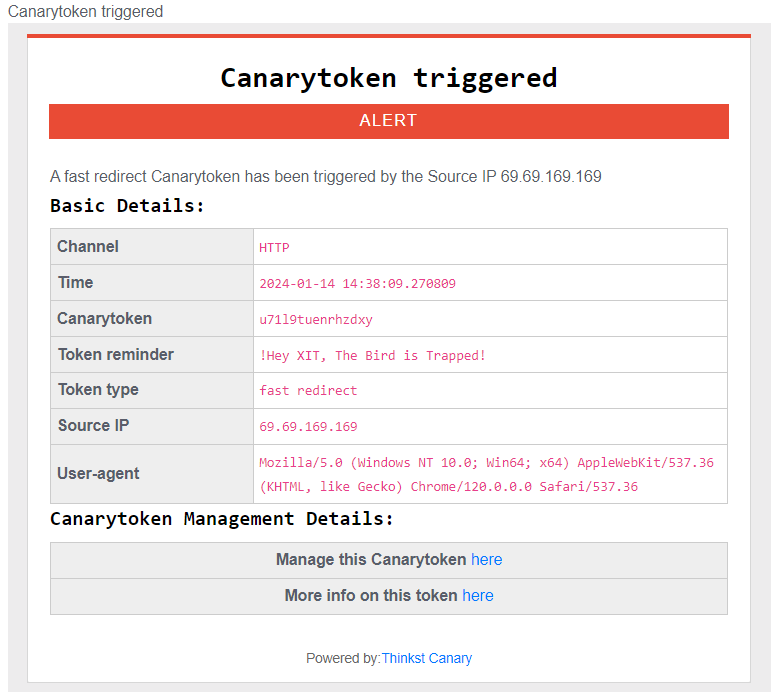
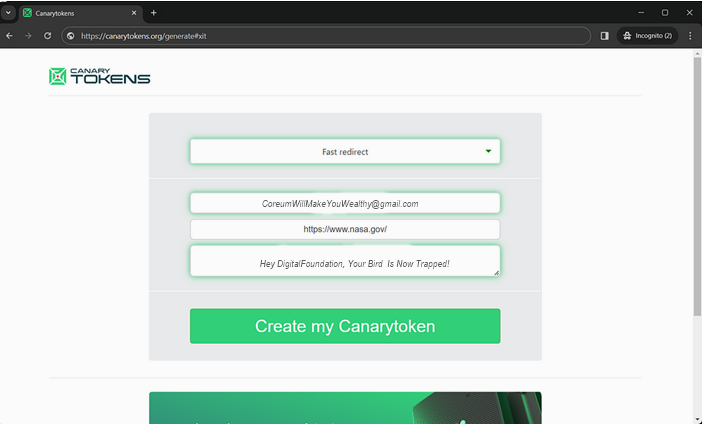
- It opposes data harvesting, ads, and trackers (even the subversive tracking that comes from opening third-party-hosted images)
- It falls under Switzerland’s privacy jurisdiction and isn’t subject to US surveillance
- Theoretically, no other human can view your emails. In fact, if you lose and need to reset your password, you’ll lose access to previous messages, an impressive layer of security against hacking
- Support for end-to-end encryption between Proton users and password protection for external emails
- A complete, constantly improving feature set, including cross-platform apps, cloud storage, and a calendar
- Open-source encryption (including optional PGP signing) and independent auditing to ensure strict adherence to standards
A few clicks, and I never have to access my Gmail page again
Compared to my first brief look years ago, Proton’s UI and general implementation have matured significantly. It was also a breeze to sit back and observe how easy it was to have over 100 (128 and counting!) forward over 100 (121 and counting!) of my Client’s perform the action of transferring each of their current Gmail messages to their now-primary Proton address, and the calendar appears to have integrated well, with alerts showing up consistently on both Android and iPhones without problems.
They are perfectly happy with the features provided by Proton’s most affordable tier, the Mail Plus plan. You can create 10 separate addresses and even a custom domain, as well as shorten the default existing domain to pm.me (because @protonmail.com is, admittedly, a bit of a mouthful).
It includes 15GB of storage, unlimited folders and filters, and can do everything I ever wanted my Gmail account to do. Most importantly, it keeps their permanent correspondence out of Alphabet’s umbrella and especially any private or confidential emails, as well as people who send it to them that don’t even use Gmail!
Proton offers diverse Subscription Plans (including Free!)
You can actually use Proton Mail entirely for free, although it does have restrictions: You are limited to 150 emails per day and 1GB of storage, can’t create custom addresses or domains, and won’t have access to the calendar, or the encrypted password manager and unlimited VPN offered by the Proton Unlimited subscription. But even the free tier is visually and more private and securr, as well as overall being much better than Gmail.
Committing to 1 or 2 years of the $5/month low tier drops the price to $4 or $3.50, respectively.
The Unlimited tier will set you back $10 or $8 per month at those same subscription lengths and afford you 500GB of storage, 15 custom addresses, 3 custom domains, and unlimited VPN and Proton Pass (its password manager) access. There is also a six-user family plan starting at $30 and three tiers of slightly more business-focused options.
But I’m really not advertising for Proton here. I’m just choosing to actively take my digital footprint back into my own hands in a way many of us haven’t done since Gmail’s massive rise over a decade ago. It’s well overdue, and over the few weeks I’ve used Proton Mail full-time, I can’t say I regret it or will ever look back.
COMMUNICATION
Price: Free
4.4




 EXAMPLE
EXAMPLE